See it in action.
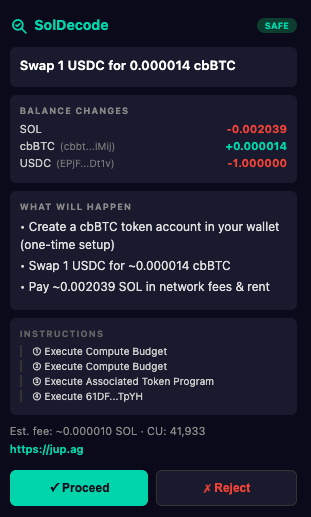
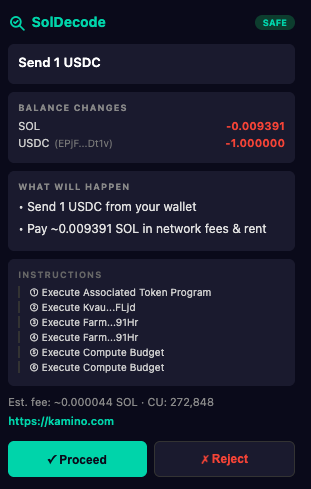
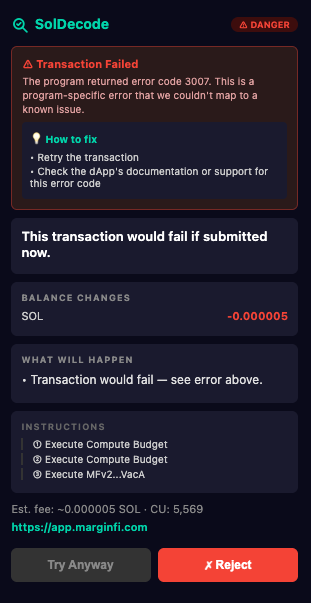
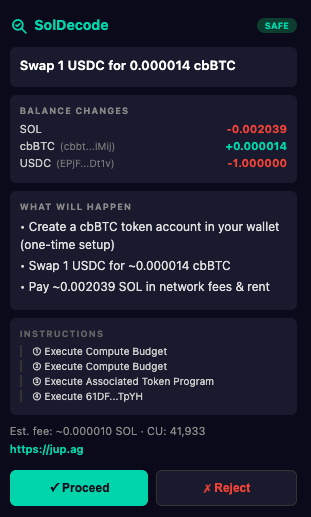
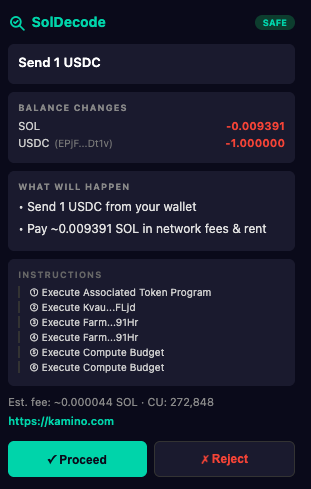
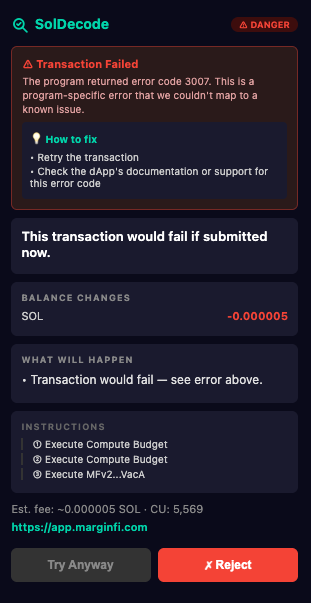
A Chrome extension that intercepts wallet sign requests, simulates the transaction on-chain, and shows you exactly what will happen to your wallet - so drainers and rugs never make it past the preview.
Every instruction is parsed from the raw tx bytes. Drainers and rugs can’t hide behind obfuscated logs because we never look at logs.
Flags any Approve or ApproveChecked instruction with amount u64::MAX - the canonical “drain my wallet forever” permission used by every phishing kit.
Detects transactions that would wipe ≥95% of any token or SOL balance, regardless of which program is doing the draining.
Catches fake USDC/USDT/JUP tokens, including Unicode spoofs like Cyrillic С and fullwidth USDC, by matching against a canonical mint table.
Flags outgoing transfers whose destination looks like but isn’t an address you’ve previously sent to. Catches Phase 2 of the poisoning attack.
After you sign, the extension polls the chain and compares the actual balance changes against the simulation. ≥5% drift fires a warning toast.
Transactions that set priority fees ≥0.05 SOL to silently siphon SOL via the fee mechanism.
One-click install from the official Chrome Web Store. Auto-updates as new versions ship.
git clone https://github.com/jvr0x/soldecode-extension
cd soldecode-extension
npm install && npm run buildThen open chrome://extensions, enable Developer mode, and click Load unpacked on the dist/ folder.
Requires a Helius RPC endpoint - get one free.